Detailed service coverage
What each service is built to do
These descriptions are structured to make scope, intent, outputs, and methodology clearer for buyers, internal teams, procurement, and assurance stakeholders.
Web Application Penetration Testing
Designed for websites, SaaS platforms, internal portals, dashboards, and business applications where route behaviour, workflows, session state, and access controls matter as much as surface-level inputs.
Our web application penetration tests use structured, evidence-led methodology aligned to PTES and OWASP guidance, including OWASP WSTG and control-informed validation against OWASP ASVS where relevant. Findings are documented using industry-standard severity and weakness taxonomies such as CVSS and CWE, with reporting structured in a clear, CREST-style format.
Routes and workflows
Access control review
Session and trust analysis
- Assessment of authentication, session controls, and route handling
- Testing of privileged functionality, user separation, and workflow trust assumptions
- Validation of exploitable findings with practical evidence and impact context
- Suitable for customer-facing, internal, and role-based applications
API Security Testing
Focused on how services actually behave under normal and hostile conditions, including endpoint exposure, access boundaries, data handling, parameter behaviour, and business logic at the API layer.
Our API penetration tests use structured, evidence-led methodology aligned to PTES and OWASP guidance, including API-specific coverage shaped by the OWASP API Security Top 10. Findings are reported using consistent severity and weakness taxonomies, with evidence designed to support triage, engineering action, and follow-on validation.
REST and GraphQL
Endpoint exposure
Authorisation validation
- Review of documented and observed endpoints across relevant trust boundaries
- Assessment of authentication state, access controls, and object reference handling
- Testing of API-specific weaknesses including exposure, misuse, and control failures
- Useful for modern apps, integrations, mobile backends, and service-driven platforms
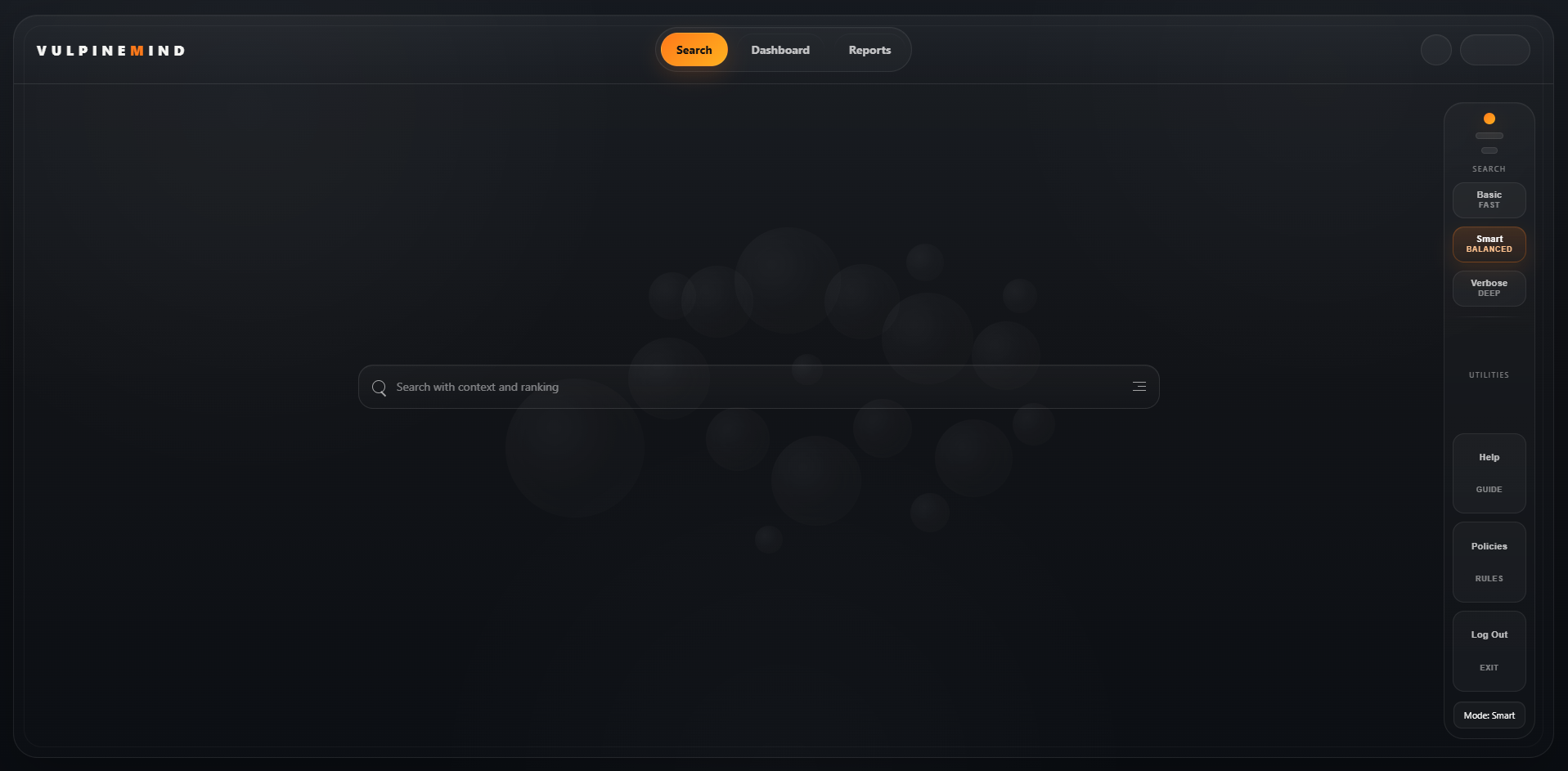
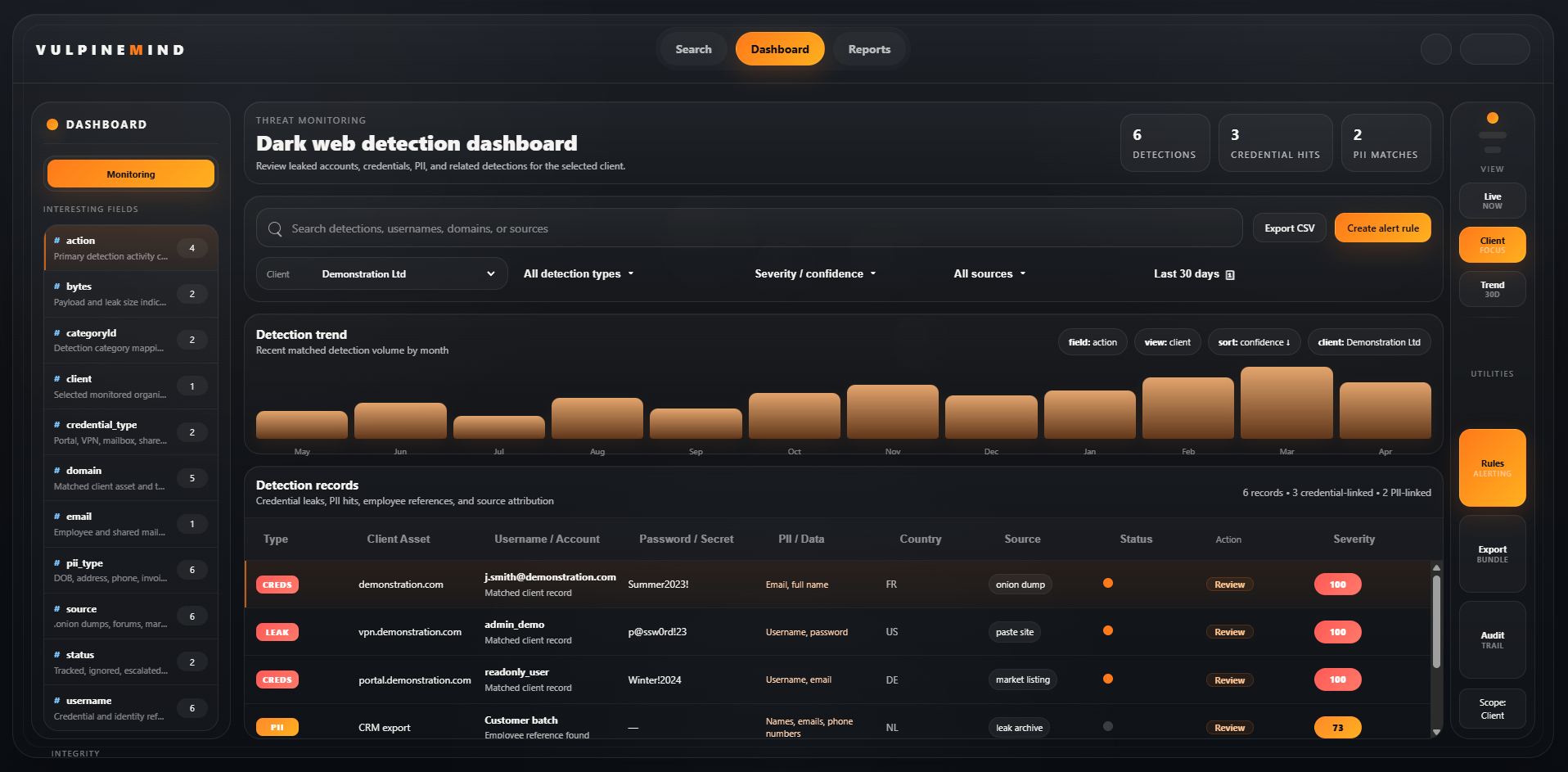
Exposure Intelligence Powered by VulpineMind
Exposure on underground sources can change an organisation’s risk profile before a formal incident is declared. This service is designed to give earlier visibility into compromised identities, leaked credentials, exposed employee references, domain and brand impersonation, exposed datasets, and mentions of organisational infrastructure across relevant hidden or criminal ecosystems.
Powered by VulpineMind, the focus is not raw noise but prioritised intelligence that can be triaged and acted on. Analysts can pivot between live manual research and continuously collected intelligence in one workflow, using validation, ranking, and correlation to turn observed exposure into something operationally useful.
Credential exposure
Leaked data visibility
Impersonation monitoring
- Monitoring for exposed credentials, identity references, and compromised user records
- Visibility into leaked datasets, breach artefacts, underground chatter, and source references
- Detection of domain, brand, and executive impersonation indicators relevant to fraud or abuse
- Actionable alerting with triage context to support containment, investigation, and escalation
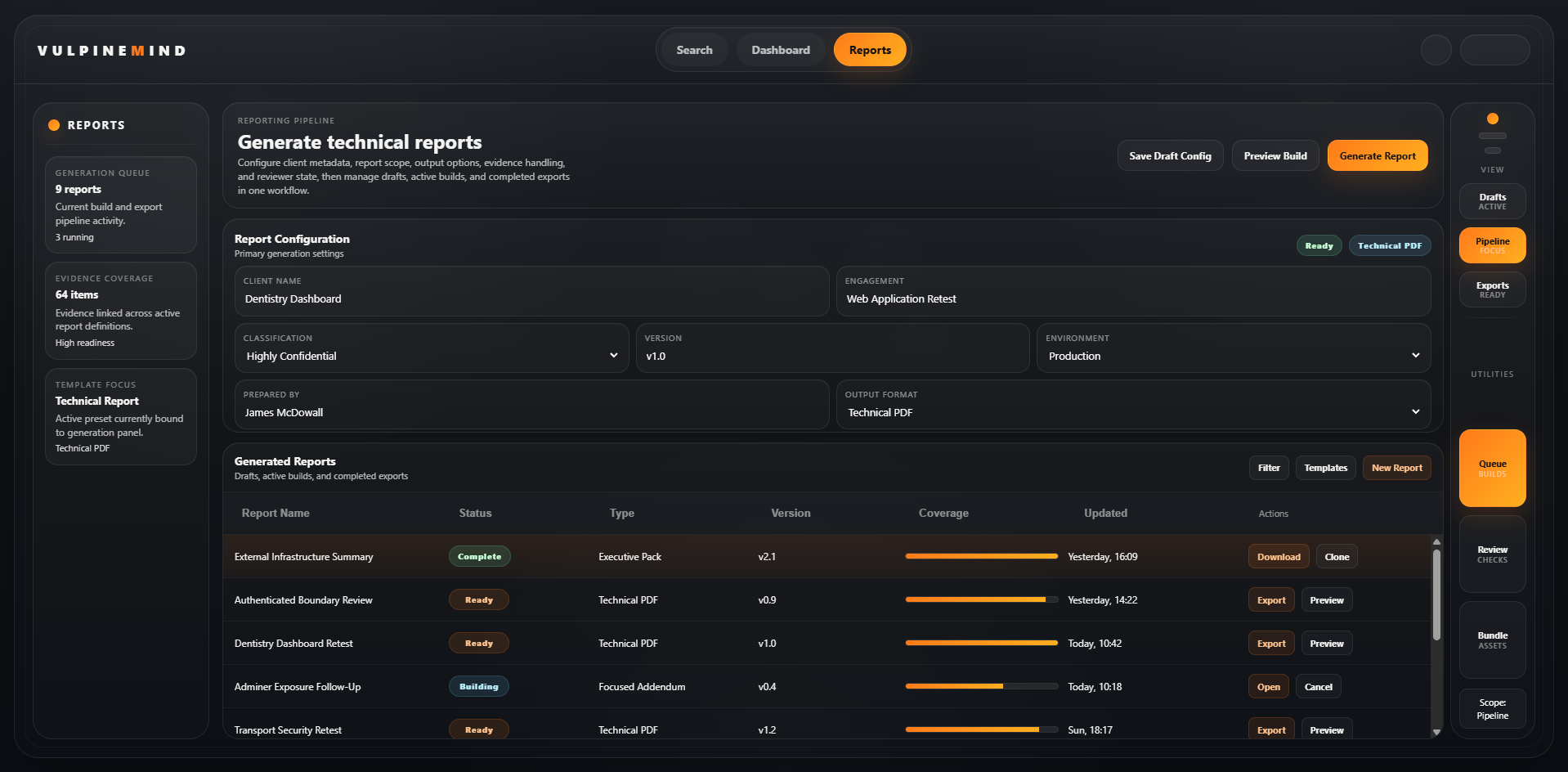
Retest Validation and Technical Assurance
Retests should do more than mark issues as fixed. They should confirm whether the original weakness is resolved, whether related paths remain exposed, and whether remediation meaningfully reduces risk.
Our retest and assurance work is designed to support technical teams, stakeholders, and governance requirements through clear validation logic, evidence of outcome, and concise reporting on fix status, residual exposure, and any follow-up required.
Fix validation
Residual risk review
Actionable outcomes
- Validation of remediated findings using targeted retest activity
- Review of residual exposure and nearby control gaps where relevant
- Clear outcome status for technical teams, stakeholders, and audit follow-up
- Useful after remediation windows, sprint delivery, or formal finding closure